In today’s fast-paced digital economy, financial transactions rely heavily on credit and debit cards. Whether for online shopping, subscription services, travel bookings, or bill payments, these cards offer bclub convenience and efficiency for consumers and businesses alike. As digital payments become more widespread, however, the need for security and management tools has grown significantly. Within underground carding communities, platforms like BClub have been discussed in forums and online discussions, often accompanied by phrases such as “BClub Dashboard: Manage Your Premium Card Access with Ease.” While these platforms operate outside legal frameworks, understanding their structure and the risks involved can provide valuable insight into the broader issues surrounding card fraud and cybersecurity.
This article explores the concept of card management dashboards, the types of data involved in underground carding platforms, the methods used to acquire this information, and the steps that legitimate consumers can take to protect themselves in the digital payment ecosystem.
Understanding Card Management Platforms
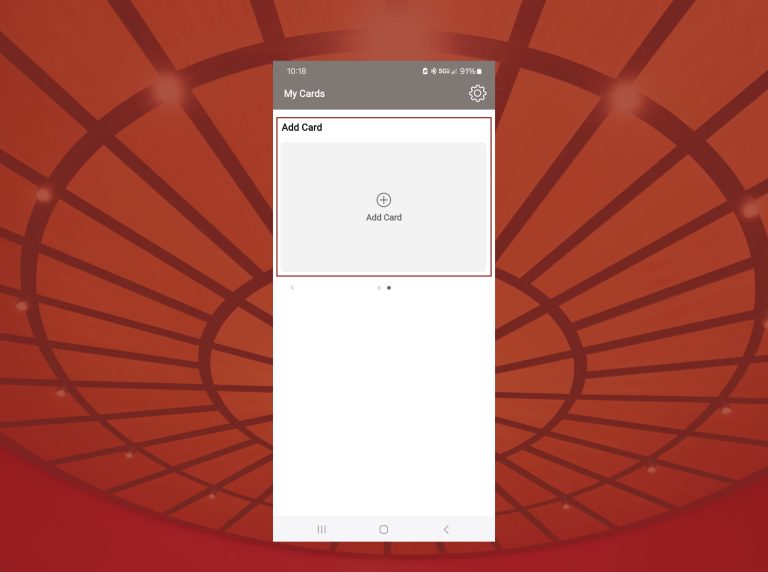
A card management platform is typically designed to organize and control access to financial accounts or card information. In legitimate banking and payment systems, dashboards allow users to monitor transactions, view card balances, enable security features, and manage account preferences. They provide a central hub for overseeing financial activity, offering transparency and control to users.
In the context of underground carding platforms, terms like “dashboard” are used to describe an interface where users can access and manage listings of stolen card data. These dashboards often mimic legitimate financial software in structure and design, providing features such as:
- Account creation and login systems
- Browsable card databases
- Search and filtering tools to locate specific types of cards
- Automated transaction and payment systems
- Vendor ratings and user feedback mechanisms
While the interface may seem professional, it is important to remember that these platforms operate illegally, and participation carries significant legal risks.
Types of Card Data Available
The main types of card information traded on these platforms usually include dumps and CVV2 data.
Dumps are data extracted from the magnetic stripe of a credit or debit card. The stripe contains encoded information used in traditional swipe-based transactions. Criminals can sometimes write this information onto blank cards to create clones, which may be used in certain in-person payment scenarios.
CVV2 data refers to the card verification value printed on the back of a card. This code is often required for online purchases and serves as an additional layer of security. When CVV2 data is stolen along with card numbers, expiration dates, and cardholder names, it can be exploited for fraudulent online transactions.
These types of card data are considered sensitive and illegal to possess or distribute without authorization. Their circulation in underground markets is a key driver of financial fraud worldwide.
How Card Data Is Obtained
Stolen card information is typically obtained through various cybercrime techniques. Understanding these methods can help highlight the importance of cybersecurity in legitimate contexts.
Data Breaches
Hackers often target large organizations such as retailers, financial institutions, or online service providers. If attackers gain access to internal systems, they can steal entire databases containing payment card information.
Point-of-Sale Malware
Point-of-sale systems in stores process card payments in real time. Malware installed on these systems can capture card details during transactions and transmit the information to attackers.
Skimming Devices
Criminals sometimes place skimming devices on ATMs or payment terminals. These devices record magnetic stripe information when customers swipe or insert their cards.
Phishing Attacks
Phishing campaigns are designed to trick users into providing their payment details through fraudulent emails or websites. Attackers often impersonate legitimate companies to make these scams appear authentic.
Once stolen, this information often circulates across multiple underground platforms, increasing the scale of financial fraud.
Cryptocurrency and Underground Transactions
Cryptocurrency has become a standard form of payment for many underground digital marketplaces. Digital currencies offer users privacy and decentralization, making transactions more difficult to trace through conventional banking systems.
Many underground platforms integrate cryptocurrency wallets into their dashboards, allowing users to deposit bclub.tk funds and make purchases anonymously. Some also include escrow features that temporarily hold funds until both parties confirm a transaction is complete.
While cryptocurrencies provide certain privacy advantages, law enforcement agencies have increasingly developed blockchain analysis tools to trace illicit financial activity, highlighting the risks of engaging in these marketplaces.
Legal Risks and Consequences
Participation in platforms that trade or manage stolen card data is illegal in virtually all countries. Laws governing financial fraud, identity theft, and unauthorized access to computer systems carry severe penalties.
Individuals caught engaging in such activities may face imprisonment, fines, and permanent criminal records. Law enforcement agencies worldwide collaborate to investigate and dismantle illegal carding networks, often targeting both operators and users of these platforms.
Understanding the legal risks is crucial: regardless of how professional or “dashboard-like” a platform appears, involvement in illegal card data management is highly punishable.
The Economic Impact of Card Fraud
The circulation of stolen card information has widespread effects on consumers, businesses, and financial institutions.
Consumers face unauthorized transactions, account freezes, and the inconvenience of replacing cards. Identity theft can have long-lasting consequences beyond immediate financial loss.
Businesses experience losses due to chargebacks when fraudulent purchases are processed. Excessive chargebacks can also increase payment processing fees and negatively impact a business’s reputation.
Financial institutions must invest in fraud detection systems, cybersecurity measures, and customer support infrastructure to mitigate losses. Globally, payment card fraud results in billions of dollars in losses every year.
Advances in Payment Security
To combat card fraud, the financial industry has implemented multiple security measures:
- EMV chip cards create unique transaction codes for each purchase, making cloning of cards more difficult.
- Tokenization replaces sensitive card numbers with secure tokens for online transactions, protecting the original data.
- Two-factor authentication adds an extra layer of verification for online purchases.
- AI-driven fraud detection monitors transactions in real-time, identifying suspicious patterns and preventing unauthorized activity.
These innovations significantly reduce the risk of fraud and improve consumer confidence in digital payment systems.
Protecting Your Financial Data
Consumers can take several proactive steps to secure their financial information:
- Monitor bank and credit card statements regularly for unauthorized transactions.
- Enable real-time alerts for card activity to detect suspicious purchases immediately.
- Avoid entering payment details on untrusted websites and exercise caution with emails requesting financial information.
- Use secure networks, strong passwords, and updated security software to protect personal devices.
By combining vigilance with secure technology, individuals can minimize their exposure to financial fraud.
Conclusion
The phrase “BClub Dashboard: Manage Your Premium Card Access with Ease” reflects the way underground carding platforms present themselves as organized, professional, and user-friendly. While these platforms may appear sophisticated, their operations involve illegal activity, including the theft and distribution of sensitive financial information.
Understanding how these dashboards function and the risks associated with them highlights the importance of cybersecurity, responsible financial practices, and legal compliance. Advances in security technologies, public awareness, and strong fraud prevention systems are essential for creating a safe and secure digital financial ecosystem.
By remaining informed and cautious, consumers and businesses can continue to enjoy the convenience of digital payments while protecting themselves from the dangers posed by illegal card data markets.